I have been using Amazon S3 storage for well over an year now and I totally love the service. However, today I had a situation where I had to give access to a single S3 bucket (the AWS account has a lot more S3 buckets) to a particular user. So, turns out, you can use Amazon Identity and Access Management for this. What IAM does is, it lets you create users and/or groups with their own security credentials and password, using which the users can access your AWS account and its services based on what permissions you allow. Normally, if a user only needs to access the S3 bucket, they would only need the AWS Access Key and the Secret key which gets generated every time you create a new user. However, if you also want them to be able to login to the AWS Management console, they are also going to need a password which can be explicitly set as it’s not set by default while creating a user.
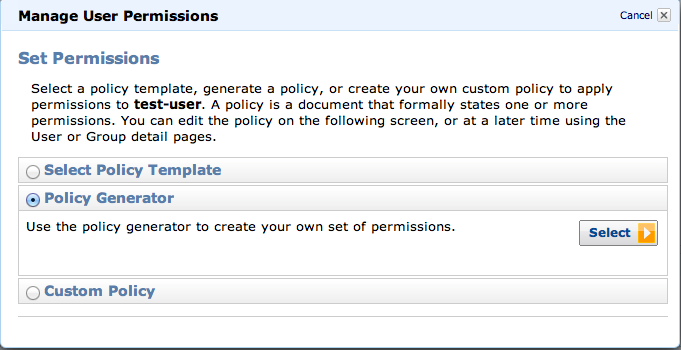
Creating a user and/or group is the easy bit. You can do it from your AWS Management Console. However, you then need to give permissions to the user to give them the right kind of access to your AWS account. I was simply trying to give this user access to one particular S3 bucket. Based on what I found out, this was as simple as creating a User Policy. So, in your management console, you will find a button to do this. Here is how it would look like :-
You need to select the “Policy Generator” as the default Policy templates only allow full or read-only access to all of S3, not just one bucket. Once you do this and select S3 service in the list of services and generate the Policy, it should look more or less something like this :-
[js]
{
"Statement": [
{
"Action": "s3:*",
"Effect": "Allow",
"Resource": [
"arn:aws:s3:::my_bucket_name",
"arn:aws:s3:::my_bucket_name/*"
]
}
]
}
[/js]
At this point, I thought, that was it. However, I was still not able to access the S3 bucket using the security credentials for this user. Apparently, what happens is that a call to connect to a bucket is preceeded by a call to List all Buckets. And since this user does not have the permission to list all buckets, the “AccessDenied” error would keep coming up when you try to connect. So, to solve this, you need to add another User Policy to this user that allows it to list all the buckets. That policy looks like this :-
[js]
{
"Statement": [
{
"Effect": "Allow",
"Action": "s3:ListAllMyBuckets",
"Resource": "arn:aws:s3:::*"
}
]
}
[/js]
So, now I have 2 policies for this user. And now I can successfully connect to the S3 account as this user. I can see all the buckets but only the one defined in the first policy is accessible to me. Others, I can’t access.
That’s it for this post 🙂





You can also use S3 Browser Freeware for to easily share your bucket with someone else.
It has an very easy to use Bucket Sharing Wizard – this is IAM based tool that automates all of the tasks described above.
It allows you to create IAM user automatically, automatically generate and apply policy.
You can find more detailed information here: http://s3browser.com/iam-bucket-sharing-wizard.php
I wanted to give access to a specific bucket to a developer, but kept getting access denied. Thank you very much for the helpfull post
Glad the post was useful
this was very useful. is there any way to do this where the users can only see the buckets that they have access to? i don’t want users to be able to see all the other buckets.
thanks so much
[…] 2nd, 2012 by admin S3 bucket https://www.anujgakhar.com/2011/11/09/giving-access-to-a-single-s3-bucket-using-amazon-iam/ IAM credentials […]
Concatenate them:
{
“Statement”: [
{
“Effect”: “Allow”,
“Action”: “s3:ListAllMyBuckets”,
“Resource”: “arn:aws:s3:::*”
},
{
“Effect”: “Allow”,
“Action”: “s3:*”,
“Resource”: [
“arn:aws:s3:::BUCKET”,
“arn:aws:s3:::BUCKET/*”
]
}
]
}
i don’t want users to be able to see all the other buckets.
theres no way around that as of right now
Perfect! I was having a hard time to solve this issue. Thank you.
I do the same, but it works if I only put objects using putObjectAcl with public-read headers. Is it possible to avoid making objects public?
Thanks for that, works perfectly!
[…] y detalles: Hosting Maven repository on Amazon-S3 Giving access to a single S3 Bucket using Amazon IAM Maven Wagon for Amazon […]
I cant seem to get this to work if I use the following
{
“Version”: “2012-10-17”,
“Statement”: [
{
“Effect”: “Allow”,
“Action”: [“s3:ListAllMyBuckets”],
“Resource”: “arn:aws:s3:::*”
},
{
“Effect”: “Allow”,
“Action”: [
“s3:ListBucket”,
“s3:GetBucketLocation”
],
“Resource”: “arn:aws:s3:::mybucket”
},
{
“Effect”: “Allow”,
“Action”: [
“s3:PutObject”,
“s3:GetObject”,
“s3:DeleteObject”
],
“Resource”: “arn:aws:s3:::mybucket/*”
}
]
}
Anyone see anything wrong with this? When I do this I get access denied. But if I replace mybucket with a * I can access all the buckets with no problem. This would work except I want to limit the use to one bucket.
Great Worked for mr